
Advanced Guide to Good VPS Hosting
The global cloud hosting market is projected to surpass $200 billion by 2030, driven by businesses and developers seeking faster, …

The global cloud hosting market is projected to surpass $200 billion by 2030, driven by businesses and developers seeking faster, …

Content Management Systems (CMS) like WordPress are more newbie-friendly than ever, and the development of site builders and AI-powered tools …
Every successful website eventually runs into a somewhat expected problem – it starts to outgrow its web hosting plan. It’s …

Managing websites for multiple clients comes with a unique set of challenges. Digital agencies need fast infrastructure, dependable support, and …

Speeding up your online project in 2026 is no longer just a perk – it’s a core goal for any …

Many people still believe that the most savings in web hosting are made from finding the cheapest possible products and …

As a small business owner, juggling limited budgets while trying to scale your online presence can feel like walking a …
Cheap VPS hosting sounds like a great concept in theory, right? You get all the benefits of a virtual private …

In 2025, VPS hosting powers 40% of enterprise websites, with cPanel accounting for 70% of control panels due to its …
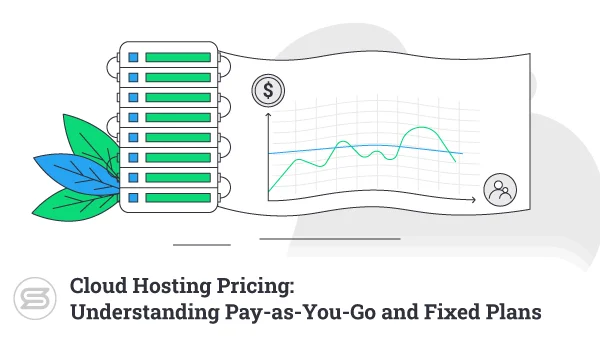
Cloud computing, more commonly referred to as simply “the cloud,” has revolutionized the tech industry. This virtual space has offered …
Getting online brings a ton of monetization opportunities. You can become a shop owner, a successful blogger, or a trusted …

Imagine you’re cruising through the vast expanse of the internet, navigating the digital highways with seamless ease. But have you …